Is AWS Really Safe? A Security Overview
A comprehensive breakdown of what makes AWS Cloud safe and secure.
I work as a Tech Arch Senior Manager at Accenture and am a mother to two wonderful kids who test my patience and inspire me to be curious. I love cooking, reading, and painting.
Recently, I attended a role-playing interview that was extremely interesting. One of the questions involved meeting an existing AWS customer, who, during our chat, voiced concerns about the security of their cloud. I delved into the topic of securing their cloud data. After a few questions, I realized the customer's concern was focused on the security of AWS infrastructure. So, here is my fresh take on this:
AWS has been named the leader in Cloud Infrastructure and Platform Services (CIPS) by Gartner for 12 consecutive years. Now, that's a huge achievement that validates AWS is at the forefront of operational excellence in securing its cloud infrastructure. This is backed by over 300 cloud security tools and the testimonials of its most sensitive customers. All this sounds great, but what exactly does this mean, and how does it translate to an AWS cloud being secure?
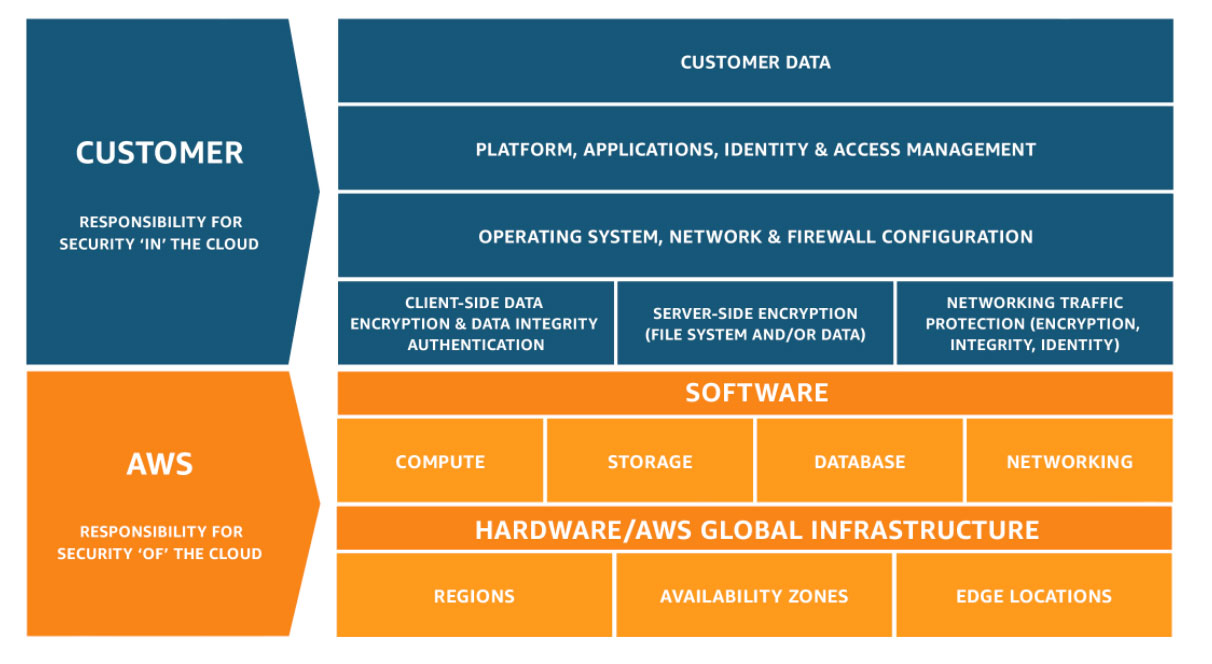
To understand this, we need to delve into the AWS Shared Security Responsibility Model. According to this model, it is clear that AWS takes sole ownership of securing the infrastructure supporting the cloud. This includes all hardware, AWS global infrastructure - regions, availability zones, and edge locations.
AWS Region consists of a collection of Availability Zones (AZ), with at least 3 AZs per region. If we look at this from an infrastructure perspective, each region is a cluster of data centres, and each group of logical data centres is defined as an availability zone. Multiple lines of proprietary high-speed fibre networks run between every availability zone, so we can treat the group of AZs as a single area. For those interested in learning more about AWS regions and which ones to choose for your project or account, read my insights here.
So, back to the question of how one knows if their cloud infrastructure is secure. In simpler words, let's take an EC2 instance, which is nothing but a virtual machine hosted on a physical machine in a data centre somewhere in the world. The customer raises concerns that the resources are on a shared infrastructure. It is very unlikely one can pinpoint the specific hardware on which the EC2 instance virtual machine is running. Because the shared infrastructure context is broader - we are talking about a specific AZ. According to our definition above, that is a group of logical data centres located within a region. This could be one or more data centres in distinct locations.
On top of this obscurity, AWS provides several security capabilities and services:
All connections throughout the AWS global infrastructure (AWS Regions and AZs) are automatically encrypted, and the connections are secured.
The spread of AWS infrastructure throughout the world limits the surface area for any DDoS attacks. Additionally, AWS is known for surviving one of the largest DDoS attacks, targeting 2.3 Tbps requests.
AWS resources can be isolated into a logical virtual network that can be defined by the customer, also known as the Amazon Virtual Private Cloud (Amazon VPC). This is secured through built-in network firewalls.
Connectivity options within the network or outside the network provide options for private or dedicated connections.
On top of the general cloud infrastructure, any software installed to support the computing, storage, database, and networking (serverless) facilities is secured by AWS through automatic software updates and security patching.
Thank you for Reading - Let's Connect!
Enjoy my blog? For more such awesome blog articles - follow, subscribe and let's connect.